Admin Login Security Extensions For Magento

This article describes a bunch of very decent Magento extensions designed to provide some extra security and protection layers as well as safety for admin login procedures.
Table of contents
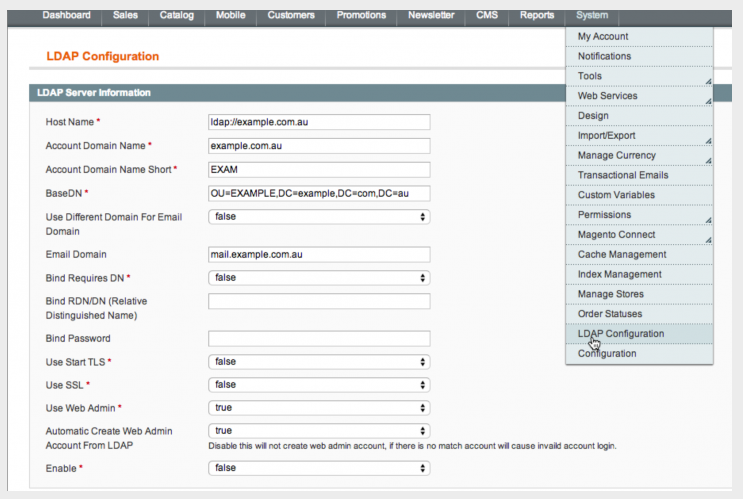
(by Magetools Kuo)
This extension developed by Magetools provides a quite comfortable interface for setting LDAP configuration as well as activating LDAP users accounts to login the admin panel.
The module does a good job allowing the field of LDAP’s department to have the auto mapped user role and is also original web administrator compatible.
LDAP settings are naturally configured with this one, also the extension supports certifated as well as anonymous bindings, multiple type LDAP, Windows and Mac systems and is enabled and disabled with ease.
It appears to be helpful if you simply need to fill your LDAP server configuration. Logging into admin panel just requires username and password set in LDAP. And while being compatible with original Magento Administrator the extension doesn’t require you to have it enabled – you can just use the LDAP setting.
All the admin functions remain to work as usual and you don’t have to support two management system accounts. Web admin accounts can be automatically created (or not – as you wish), so more control over user management is obtained.
Developers promise free full lifetime upgrades though you’ll have to uninstall old versions to install the new ones. However, you will be consulted on PHP LDAP extension free of charge.
There is a certain issue with uninstalling this extension: an attempt of performing an automatic uninstall while using the admin session occurs the cache refreshing and . The files have to be deleted manually.
First, the maintenance.cfg file has to be deleted, then cache (MagentoRoot/var/cache/*) and finally, the session (MagentoRoot/var/session/*).
LDAP Account Login as Administrator is available for $65
(by MagePsycho)

This little module is designed to help any admin user to set his locale of choice during login process. Very useful when there are several admins of one store located not in the same city. Or if you happen to be the admin having to customize the magento for a far away located store owner.
Extension has a bunch of usual features such as upgrading, easy enabling/disabling and saving locale options for next visits.

Tested for version 1.3.2.4 – 1.9
And here is a really nice thing, Admin Login Locale Selector is absolutely free of charge which means any shop owner may consider hiring admins from different places of living with absolutely no worries.
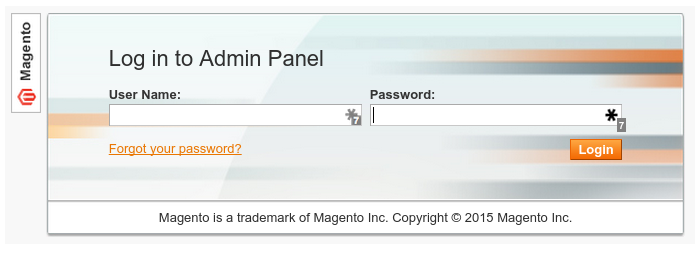
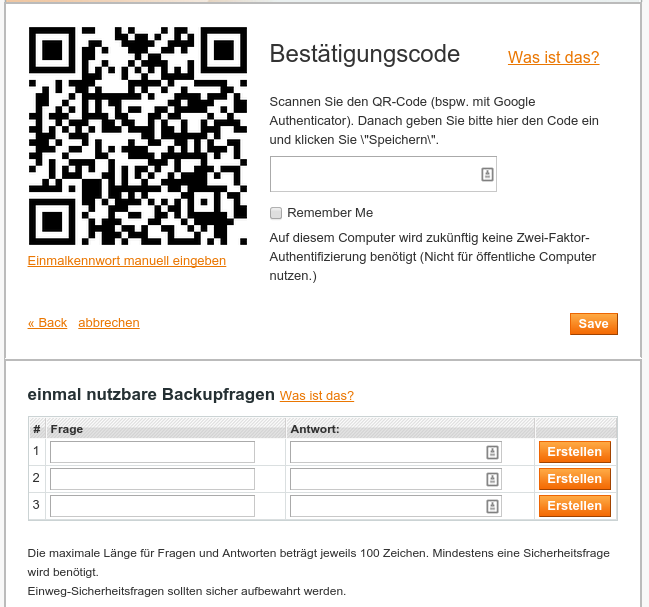
Started at January 2014 at the Magento Worldwide Online Hackathon this project is designed for extra resources protection and is using Google’s 2-Step Verification algorithm to implement s two-factor authentication.
Admins authenticate themselves via ordinary login dialog and after that Google Authenticator app generates a security code on admin’s mobile devices, then they are asked to enter this single-time code.
With this procedure you can be assured that your resources which can be accessed by admins have an extra layer of protection forbidden to any third parties. This means that your data will be secure even if your admin’s laptop is stolen.
Please have in mind that this procedure is additional and that the default login process will also be always required.
This extension can be installed in two different ways. Firstly you’ll have to install Google Authenticator to your smartphone, then install the module using Composer or modman and log into Magento admin. After that use the Google Authenticator application to scan the QR code, determine security questions and proceed to login.
Another way of installation is via Composer.
Find the require section of composer.json and add “magento-hackathon/magento-two-factor-authentication”: “*” there.
You may also open the Composer shell command and add:
composer require magento-hackathon/magento-two-factor-authentication:*
The project is running under MIT License (MIT), is still receiving updates and is being supported by community.
(SAML)
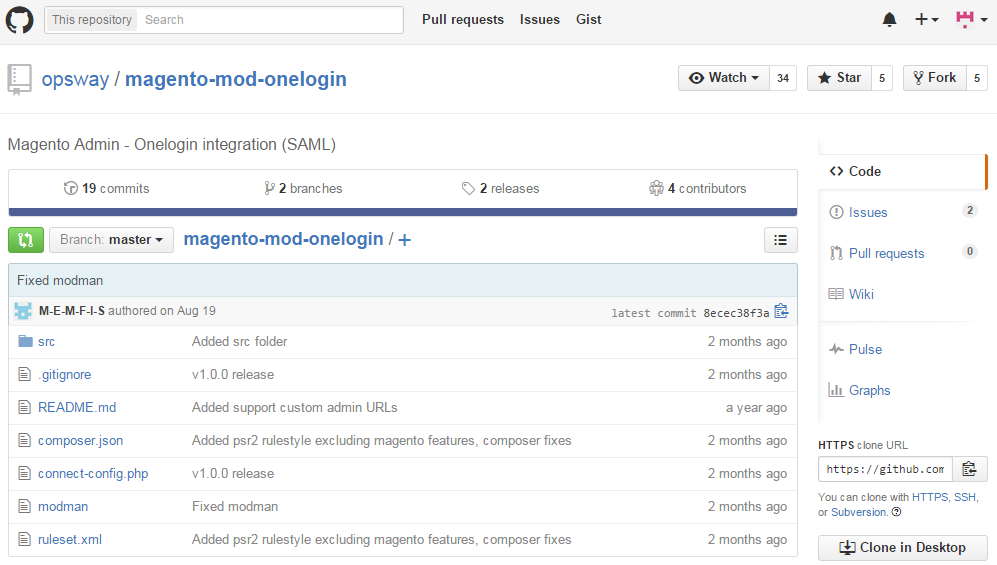
This module provides a possibility of login to Magento Admin through Onelogin Identity provider.
After extension is installed the link “Login via Onelogin” appears on backend login form. It leads to several redirects described by SAML 2.0 standart.
The user is given access to Magento after his email information has been sent there and appeared to be correct for identification.
Using this module may appear a little bit tricky but works fine if certain steps are followed. You should go to Onelogin.com and create an application, set credentials to “Shared” status and enter the email address intended for letting all users to login to a single Magento account. After that, application ID and X.509 certificate should be copied. Then the module can be copied to Magento folder where it becomes configurable – just go to System->Configuration->Developer->Onelogin and enter the needed settings. Then Magento settings should be flushed and that’s it – click “Login via Onelogin” and proceed with your work.
Onelogin module is capable of automatic user creation based on IdP supplied data. To activate this feature you should enable System – Configuration – Developer – Onelogin – Create. Magento’s fields should be mapped to Onelogin ones. Consider taking into account these common ones:
- Username: User.Username
- Email: User.email
- First Name: User.FirstName
- Last Name: User.LastName
- Role: memberOf
There is a certain restriction for a user auto-creation. It cannot happen if the needed attributes aren’t provided by the IdP but if the account already exists, you will just have to enter the email to log in.
So in the process of new account creation Magento tries to map the role provided by Onelogin to its own, Magento role. And if the names are different, module lets you to map them and you’ll have three fields to map these pairs. Also, it is able to map a whole pack of separated by comma Onelogin roles to a single Magento role.
User may be prevented from accessing the admin panel if the associated Magento account doesn’t have the administrator Magento role.
Supports Magento CE 1.4+ and Magento EE 1.9+
and
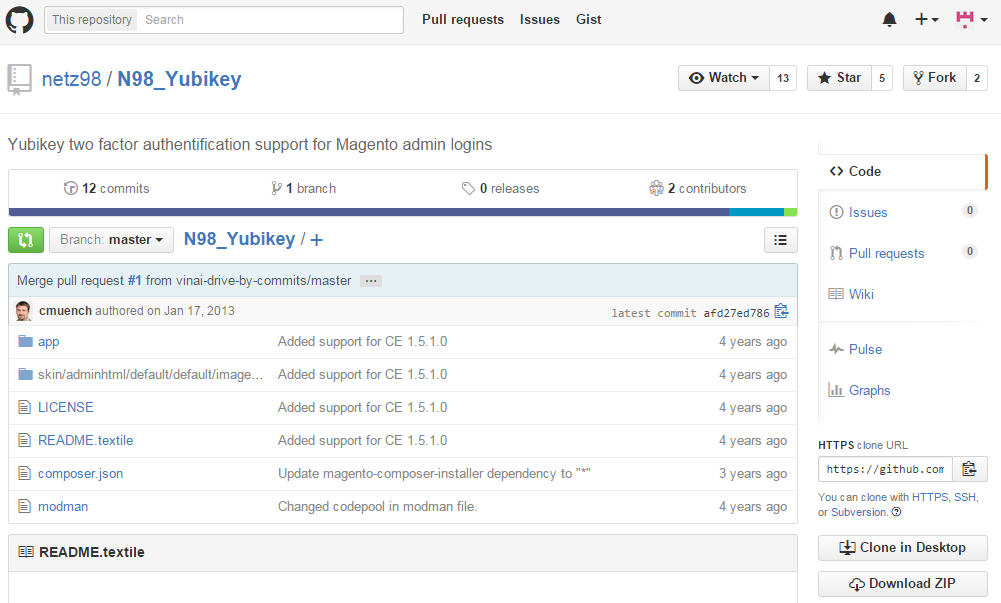
One of the most effective and easy-to-use tools, yubikey, is a small hardware device that simplifies access through all the multi-layered protection systems just to one single touch of a button.
The device is strong enough to be used by largest enterprises yet really simple to be operated by any person. There are both contact and contactless options to communicate with YubiKey: USB or NFC/MIFARE. One security key is able to support a huge number of applications, no drivers neither software, SMS-like passcodes to retype or batteries are needed. FIDO U2F, Yubico-OTP, OATH-OTP, OATH-HOTP, OATH-TOTP, OpenPGP and PIV are officially supported.
There are several versions of YubiKey to choose from, starting from $25/key basic one to YubiKey NEO $50/key premium which includes PIV-Compliant Smart Card, OpenPGP, and FIPS 140-certified with CCID Smart Card.
To add a yubikey login for magento all files should be placed into magento root folder. And using a modman is effective because this extension is modman enabled. After install is complete the yubikey authentification should be enabled for admins. Just go to System Configuration- Admin-Yubikey, and enable yubikey. Then enter client id (register it at https://upgrade.yubico.com/getapikey/ if you need) and type your Magento shop’s secret.
Next step is adding yubikey to admin user. After enabling the service a yubikey id should be added to each user, and for that open System-Permissions-Users, then select the user and user edit form should appear. It has this new tab for the yubikey configuration. Lastly, add the needed yubikey to the user. Please be attentive to assign the correct yubikey id to the appropriate user or otherwise you may block yourself and will have to reset yubikey id in the database.
—
There are many Magento extensions out there but these appear to be very special because they are the ones that guarantee the safety of your business. From small software solutions to more complex (yet simply to use) accompanied by hardware devices these extensions should be necessarily taken into consideration since they are the essential part of every successful Magento store.